The phone number that can empty your wallet
Data goes silent. But somewhere else, another device may now be receiving the verification codes meant for you. That is when the real damage begins.
By Wilfred M Kahlari
3h ago
How scammers execute fraudulent transfers from firms to their accounts
The unsuspecting employee processes the transfer, believing it to be a legitimate request; and
By Jacob Mutisi
Feb. 28, 2025
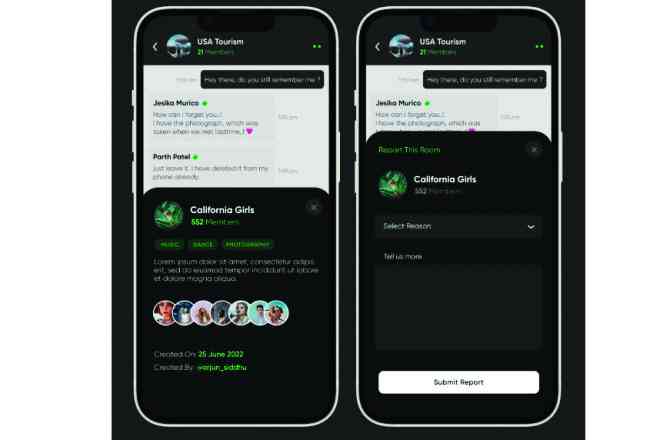
Protect yourself on the cyber space
Cloned websites and apps are fake versions of real platforms, designed to look identical to trusted services like banking, shopping or government portals.
By Jacob Mutisi
Nov. 1, 2024